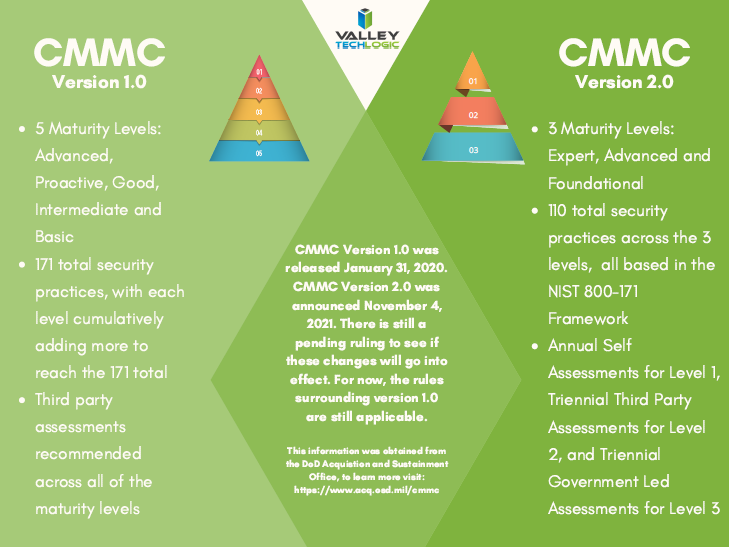
Last week we covered a general overview of what the Cybersecurity Maturity Model Certification (CMMC) program is and what’s been announced for 2022 so far. Presently, there are five maturity tiers found in program, although if (or when) version 2.0 is released it’s been announced that the program will be simplified down to just three tiers.
The changes that will be happening with version 2.0 however don’t affect tier one very much. Tier one covers basic cybersecurity hygiene in both versions of the program. It sets the groundwork for the later tiers and while the topics covered are “basic”, the foundational coverage they provide is imperative for any business – not just those required to adhere to CMMC for contractual or compliance reasons.
The Cybersecurity Maturity Model Certification (CMMC) program includes 17 controls at the moment with 171 practices. Thirty of those practices are only found within CMMC and not in the framework which formed the basis for it (NIST) and are anticipated to be removed in version 2.0. However, in both version 1.0 and 2.0 there are 17 practices that must be adhered to for tier one.
It’s important to note as well this process is not one and done, you must actively maintain your cybersecurity compliance to continue being certified within CMMC. Failure to do so could result in losing your certification, losing contracts that require CMMC compliance, and or even being fined for violating the False Claims Act (FCA) which will talk about in more detail in a future article.
It’s beneficial to maintain your compliance to both adhere to the program and protect your business from cyber threats.
In tier one the program begins with “Access Control” and there are five components. These components cover topics such as user privileges and controlling remote access and access to internal systems.
The next control is “Identification and Authentication” which aligns well with Access Control, the two practices found within that control involve documenting those that access your systems and maintaining reports for those logins.
Then we have “Media Protection” which has just one practice and it’s aimed at maintaining sanitation of your devices (such as removing sensitive data from hard drives).
Next, we have “Physical Protection” and in tier one of CMMC this topic covers improving the way you surprise visitors to your office location (a lot of cyber threats stem from an attack known as “spear phishing”). There are four practices found under “Physical Protection”.
“System and Communication Protection” has two practices and they’re both aimed at securing the private communication you and your employees have (that may include CUI – Controlled Unclassified Information – data).
Finally, we have “System and Information Integrity” which has five practices that cover better securing your businesses systems, including performing needed updates, and monitoring for malicious code.
As you can see, these basic practices set a good baseline for activities found in higher maturity tiers. In tier one “System and Information Integrity” you’re monitoring for malicious code – in tier two and three there are practices that stipulate how to actually deal with it.
We will be continuing to provide more information on CMMC in this series, next week we will take an in depth look at tier two. If your business needs to meet the requirements for being CMMC certified, Valley Techlogic can help. We have experiences helping businesses achieve greater cybersecurity compliance and assisting them with the certification process. Learn more today.
Looking for more to read? We suggest these other articles from our site.
-
New Year, New Bugs – The Y2K22 Bug Crippling Exchange Servers
-
The 5 Biggest Mistakes Business Owners Make With Their Technology
-
Windows 10 End of Life is Coming, and It’s Sooner Than You Think
-
The Extreme Side of RAAS (Ransomware As A Service)
This article was powered by Valley TechLogic, IT service provider in Atwater, CA. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on Twitter at https://x.com/valleytechlogic.