Some fraudsters have abandoned the awkward, obvious emails of the past decade in favor of a new gambit, this one focus on social media. Today, they operate where your business already lives: in your LinkedIn inbox, your Facebook admin panel, and your Twitter DMs. The scams are polished, convincing, and growing fast.
Social engineering attacks rely on manipulation rather than malware. Instead of breaking through your firewall, criminals exploit the one vulnerability no software patch can fix: human trust. In 2024 and into 2025, that manipulation has migrated aggressively onto social media platforms, targeting professionals, business owners, and marketing teams who use these networks as core business tools.
Understanding how these scams are constructed is the first line of defense. Here is a closer look at what is circulating on each major platform and what warning signs to watch for.
LinkedIn: fake job offers and recruiter impersonation
First, The fake job offer scam.One of the fastest-growing threat vectors on LinkedIn involves fraudulent job opportunities delivered via connection requests and direct messages. Attackers create convincing recruiter profiles, complete with employment histories, endorsements, and professional headshots, before reaching out to targets with lucrative-sounding roles at legitimate companies.
Once contact is established, the “recruiter” moves the conversation off-platform to WhatsApp or email and eventually asks for sensitive information under the guise of onboarding: copies of identification documents, bank account details for direct deposit setup, or payment for background checks and equipment deposits. In some cases, victims are sent fraudulent checks and asked to forward a portion of the funds before the check bounces.
Luckily there are a few common red flags you can look for to spot this one, such as:
- The recruiter’s profile was created recently and has few connections or activity.
- The job offer arrives unsolicited with an unusually high salary and vague responsibilities.
Also, a more targeted variant involves attackers creating near-duplicate profiles of a company’s senior executives or trusted colleagues. The impersonator connects with employees and then requests urgent wire transfers, gift card purchases, or credential resets, exploiting the authority of the mimicked identity. Because the message arrives through LinkedIn rather than email, many recipients lower their guard.
LinkedIn has acknowledged the scale of fake profile activity on its platform and introduced detection tools, but sophisticated actors continue to slip through. Treat any out-of-character financial or credential request from a connection with immediate skepticism, regardless of how authentic the profile appears.
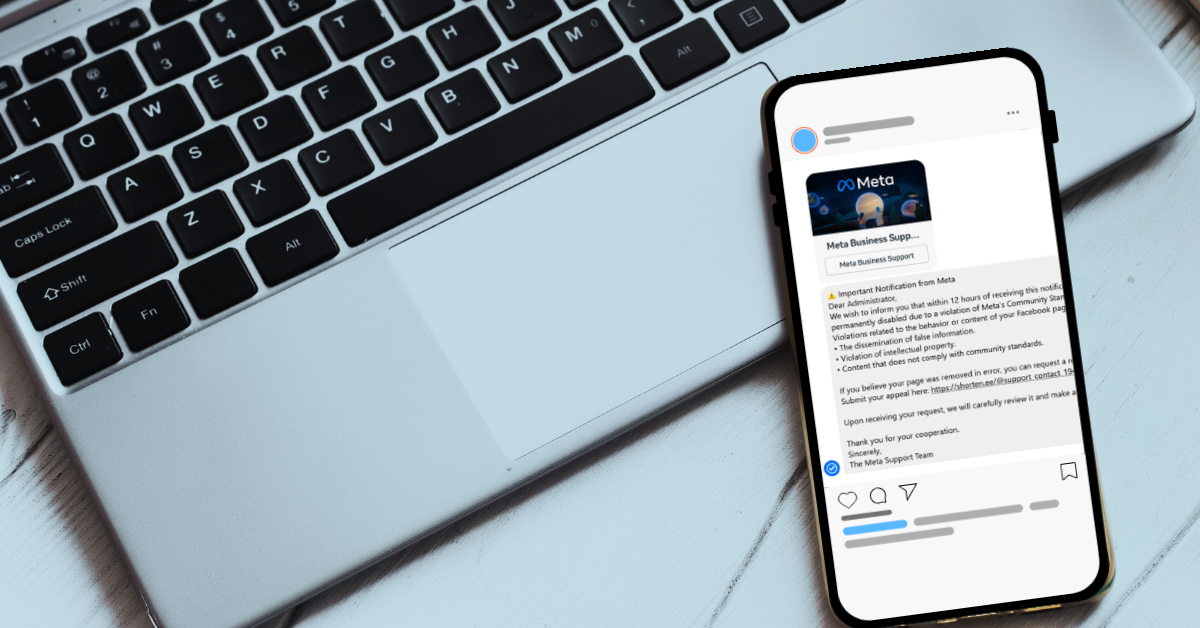
Facebook: business account threats and fake admin messages
Businesses running Facebook Pages and advertising accounts have become prime targets for a scam that impersonates Meta support. The attack typically begins with a message, often arriving via Messenger or a business inbox, warning that the page violates community standards and faces imminent suspension. Targets are urged to click a link and “verify” their account to avoid action.
Those links lead to convincing phishing pages that harvest Facebook credentials, two-factor authentication codes, and in some cases payment information linked to the ad account. Once attackers gain access, they drain advertising budgets, lock out legitimate admins, or sell the established account to other bad actors.
Common red flags for this one are:
- Urgent language around page violations sent through Messenger rather than through Meta’s official support system.
- Links that route to domains that are not facebook.com or meta.com.
A related tactic involves fraudulent invitations to become a page or group administrator. Business owners receive what appears to be a legitimate Facebook notification asking them to accept an admin role for a page they do not recognize. Accepting grants the attacker reciprocal admin access to the victim’s own pages by exploiting Facebook’s cross-admin trust structure. The scammer can then post spam, remove the original owner, or use the page for further fraud.
Meta will never request login credentials or payment information through Messenger. Any urgent policy warning that arrives as a direct message, rather than through the official Meta Business Suite notification system, should be treated as fraudulent until verified directly through Meta’s help center.
Twitter (X): impersonation, verification badge scams, and crypto fraud
Since the overhaul of the platform’s verification program, bad actors have exploited user confusion around the blue checkmark by sending direct messages claiming the recipient’s account requires action to maintain its verified status or avoid suspension. These messages direct targets to external sites that steal credentials or payment details.
A parallel scam targets business accounts with messages purporting to be from the platform’s trust and safety team, warning of copyright violations or policy breaches and requesting immediate login through a provided link. The urgency and official-sounding language make these messages disproportionately effective against small business owners managing their own accounts.
Again, common red flags are:
- Direct messages claiming to be from platform support, since X does not use DMs for official account actions
- Requests to “re-verify” through a third-party link rather than within the native app settings
Also, we want to be clear, do not overlook email: phishing remains the dominant threat and it’s also always constantly evolving.
While social media scams command growing attention, it would be a significant mistake to treat email phishing as a solved problem. Email-based attacks remain by far the most prevalent form of social engineering, accounting for the majority of successful business data breaches year after year. Modern phishing emails have evolved far beyond the broken-English missives of the early 2000s: today’s attempts accurately mimic bank correspondence, software license renewal notices, internal HR communications, and delivery notifications, often using the target’s actual name, employer, and recent activity pulled from public or previously compromised data.
Business email compromise, a targeted phishing variant in which attackers impersonate executives or vendors to authorize fraudulent payments, cost U.S. businesses billions of dollars annually. The threat is consistent, scalable, and disproportionately effective against organizations that have not established clear verification procedures for financial requests.
Staff who know to question a suspicious LinkedIn message may still instinctively trust an email that appears to come from their bank or their own CEO. Awareness training must address both channels with equal rigor.
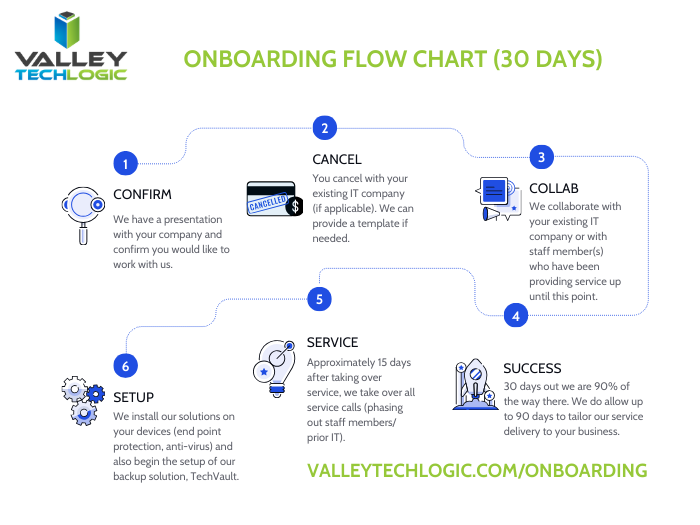
A local managed service provider like Valley Techlogic is your first line of defense.
Recognizing individual scam tactics is valuable, but the threat landscape shifts faster than most business owners can track. A local managed service provider like us brings dedicated security expertise, advanced email filtering and phishing simulation tools, and ongoing employee awareness training that keeps your team current with the latest social engineering techniques crossing every channel, from LinkedIn inboxes to email spoofing campaigns. We can also establish clear internal protocols for verifying unusual requests, configure multi-factor authentication across your accounts, and monitor for credential exposure before attackers can exploit it. Partnering with a trusted local provider means that when the next convincing scam lands in your inbox or your social feed, your business has both the technology and the training to recognize it before it does damage. Learn more today with a consultation.

- Microsoft 365, Google Workspace and.. Apple Business ? What is Apple’s new entry into enterprise software and what does it mean for your business
- So long Sora, ChatGPT pulls the plug on AI video generation platform amidst a $1 billion dollar pull out by Disney
This article was powered by Valley Techlogic, leading provider of trouble free IT services for businesses in California including Merced, Fresno, Stockton & More. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on X at https://x.com/valleytechlogic and LinkedIn at https://www.linkedin.com/company/valley-techlogic-inc/.