We’ve discussed cybersecurity training before and its importance in preventing the number 1 cause of cybersecurity disasters – human error.
We offer cybersecurity training as a core feature in our tech care plans, but many topics you can (and should) cover yourself with your employees. There couple be rules that specifically apply to your business sector; like HIPAA for healthcare or CMMC for Department of Defense contractors.
Maybe you’ve experienced a cybersecurity attack before and after the dust settled you came up with a game plan specifically to prevent it from happening again. If it hasn’t happened to you yet, it’s a mistake to assume it never will. In 2021 42% of businesses experienced a cyberattack. It’s a numbers game most won’t win without preventions in place.
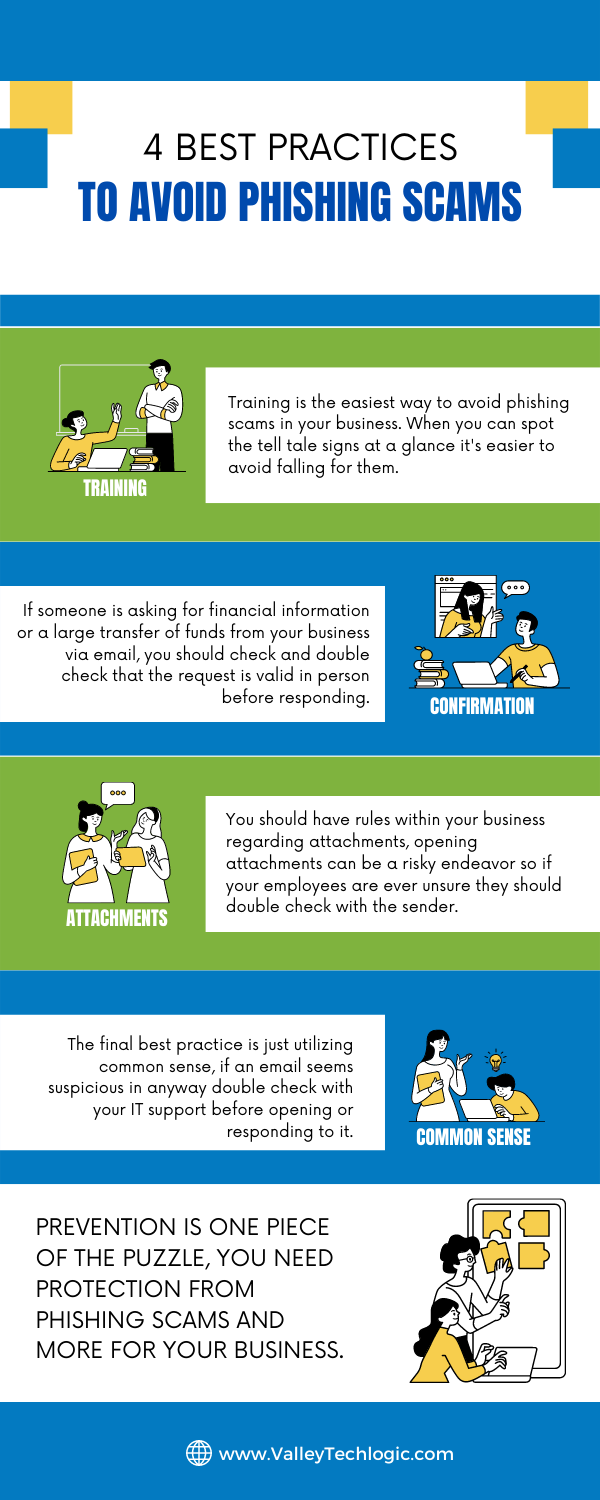
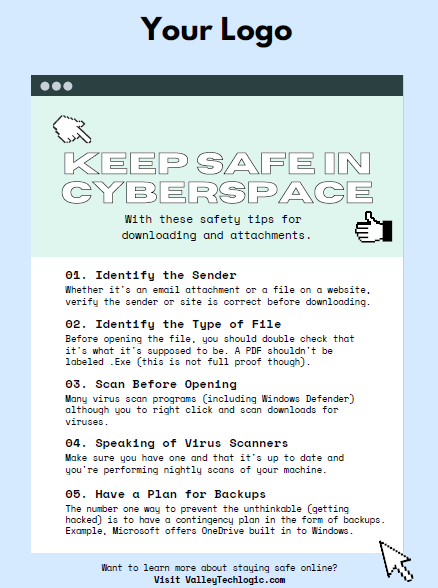
To start, we want to offer these posters we’ve created on two common cybersecurity threat topics, email and malicious attachments. These posters are free for you to print and brand to use in your office or send as a reminder, and these are two excellent places to start when you’re looking to beef up your office security.

Here are five more training topics all workplaces should also cover:
- Like our posters above, email security and having strict guidelines for attachments and downloads is one key thing to focus on in your cybersecurity training efforts.
- It’s also important to provide guidance for internet usage while at work. Many employers try to digitally lock this down, but these efforts are usually met with annoyance and disdain from employees and are often in vain. Instead of arbitrarily trying to block everything with software we suggest having guidance about what’s appropriate for work devices (and what Isn’t). We also suggest noting that even if a website looks legitimate it may not be, so they should be wary of sites that ask you to download something or enter private credentials.
- This comes to the next topic which is practicing good safety hygiene with work devices. Three easy steps are: Locking your computer when you walk away, only downloading software from work authorized sites, and keeping your device up to date with patching and software updates. They may need assistance with the third step so it’s a good idea to have your IT provider manage workstations if you’re able to (this is something Valley Techlogic providers for all clients).
- The fourth step is protecting company data. If you’re employees have to interact with documents that are confidential in nature you should have rules for the sharing of those documents, as well as a comprehensive plan for backing them up safety.
- Finally, you should provide guidance on passwords and multi-factor authentication. Having a rule in your workplace that for work accounts they must have multi-factor enabled (or have your IT team enable it across the board) will drastically improve your office’s online safety. We have guidance for this topic here.
It can feel overwhelming to have all of these topics to cover with your employees, but we cannot overstate how important it is to cover these topics with your employees, even if you think they’re things they should already “know”.
At Valley Techlogic we have partnered with a platform that not only provides cybersecurity training resources, but it also allows you the ability to create your own training modules. You can even cover topics that fall outside the cybersecurity spectrum. We can also work with your business to assist you in the creation of these training modules, if you would like to learn more schedule a consultation with our sales manager Annette today!
Looking for more to read? We suggest these other articles from our site.
-
Our UPDATED Guide to MFA (Multi-Factor Authentication)
-
How a phishing scam swindled this Shark Tank host out of $400,000
-
10 things you can do today (yes today) to make your business’s network safer
-
Our Five Best FREE Resources Ranked
This article was powered by Valley Techlogic, an IT service provider in Atwater, CA. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on Twitter at https://x.com/valleytechlogic.