Last week we touched on tips for buying new tech for your business in 2023, but for some offices BYOD (Bring Your Own Device) is the norm.
What is BYOD? Bring your own device is where an employee uses their personal device (usually a laptop) for work purposes. There are different ways to go about this, for some offices there employees using an already owned device. For others, they can use a device they own but they must log into a virtual machine to do their work. A third option is that the business still purchases the device an employee uses but because they work remotely from home the same rules of BYOD still apply even though it’s a company owned device.
During the pandemic we saw more articles related to BYOD and remote working and how to still manage a secure workspace even if your employees aren’t coming into the office. Even with workplaces now open again many are operating on a hybrid model and advice surrounding security of devices that don’t stay in one location is still very relevant.
Business owners themselves also often take their devices home with them at the end of the day and aren’t immune to the same pitfalls that can happen if you don’t have policies in place to help protect your office network and data. BYOD offers work places a lot of flexibility as long as security measures are adhered to.
Here are our tips for smart BYOD policies to have in 2023:
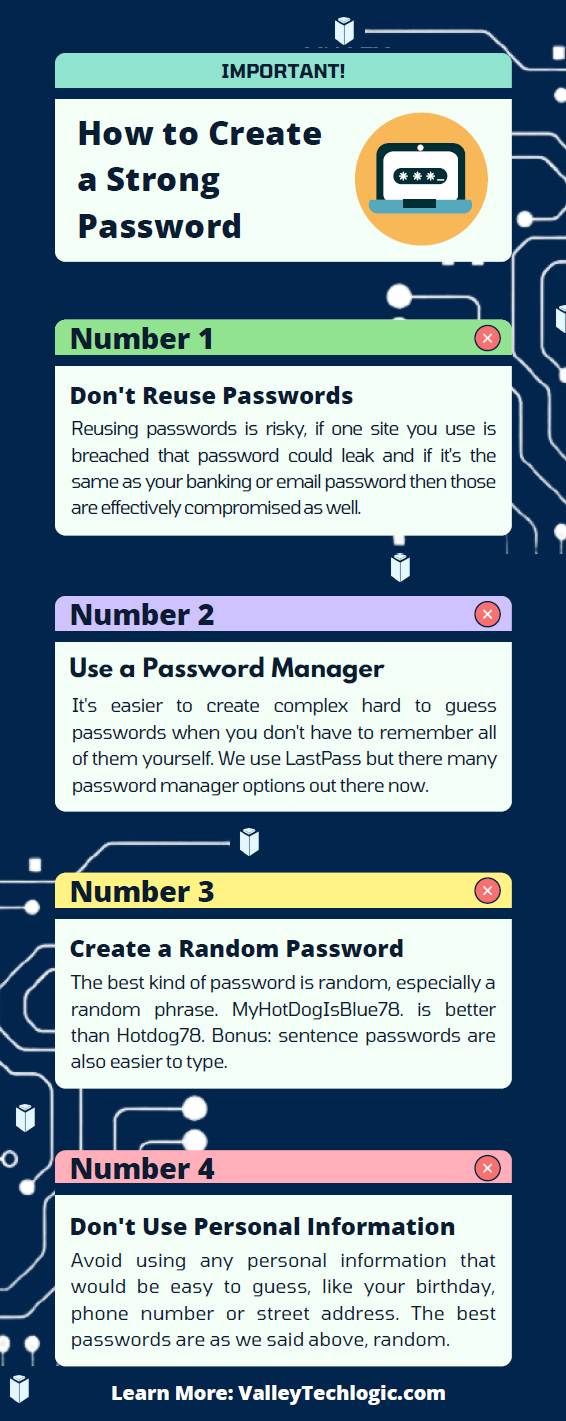
- First and foremost, have a good password policy. Especially for company websites and other logins. See our chart below for what makes a good password.
- Determine what data can be accessible from home or a BYOD. Some data should be restricted to in office/office devices only, especially anything client sensitive. You can also utilize a company SharePoint to share files without having them be locally stored on devices.
- Have time-based lock-out procedures to limit long sessions, especially if a device is idle. An idle device left in an unfamiliar place is a potential vector for hacker access. Time-based lockouts will make devices used offsite much more secure.
- Utilize the same security stack on BYOD as you do on company or office devices. Many cybersecurity tools don’t require devices to be in the same building, it’s a good policy to have your IT provider install the same tools on BYOD and other devices that leave the office. If your company uses Windows you can also consider something like Microsoft’s Intune for easier management of all of your endpoints no matter where they’re being used from.
- Have a policy for wiping company data off a BYOD. Especially if the device is employee owned, you shouldn’t assume that it will always be a smooth hand off. Having policies for this in writing is crucial.
Like we said the first step is having a good password policy is step one to a good BYOD plan for your business, and we might argue it’s the first step in a good security plan overall. Here are our tips on what makes a good password:
If you need help with device management in your business, Valley Techlogic can create a plan of action that encompasses both flexibility and security into a package with functionality at the forefront. Reach out today to learn more.
Looking for more to read? We suggest these other articles from our site.
-
Need computers for your office? Purchasing before the New Year could save your business a ton of money
-
High Tech Holidays – Five Ways Technology Can Make Your Holiday Season Easier
-
Hackers and the holidays, US government warns ransomware doesn’t take days off
-
Black Friday Isn’t just for consumer purchases, business owners can take advantage as well with these tech deals
-
10 Holiday Shopping Tips for Safer Online Shopping
This article was powered by Valley Techlogic, an IT service provider in Atwater, CA. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on Twitter at https://x.com/valleytechlogic.

