When most business owners think about security risks, they picture hackers, ransomware, or phishing emails. Those threats are real. But in many small and midsize businesses, the biggest exposure is much closer to home.
It is the former employee whose access was never fully removed.
Improper offboarding is one of the most common and most expensive security gaps we see at Valley Techlogic. A user account left active, a shared password that never changed, or a mobile device that still syncs company email can quietly create major risk months after someone leaves. If your offboarding process is informal or inconsistent, now is the time to fix it.
Why past employees are a real security risk
Most former staff are not malicious. The risk usually comes from oversight, not intent. However, the impact can be just as damaging.
Here is what commonly goes wrong:
- Email accounts remain active and continue receiving sensitive information
- Microsoft 365 or Google Workspace access is never fully revoked
- Saved credentials remain on personal or unmanaged devices
- Shared passwords are not rotated after departure
- VPN or remote access tools stay enabled
- File ownership and permissions are never reassigned
For IT staff and security teams, this is basic hygiene. But in the real world, especially in small business environments, offboarding often happens in a rush. HR processes the paperwork, IT is notified late or not at all, and access cleanup becomes partial at best. You only need one missed system to create a problem.
Many organizations assume that if the employee was trustworthy, there is little to worry about. That is a dangerous assumption. Former employee risk shows up in these five ways:
- Data exposure Old accounts can still access client files, financial records, and internal communications.
- Compliance violations For regulated industries, failure to revoke access can create audit findings or legal exposure.
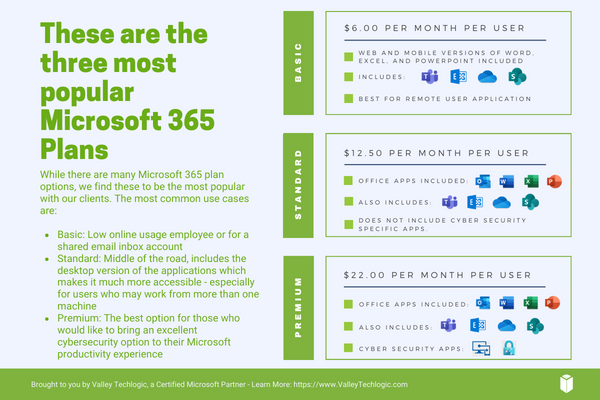
- License waste From a Microsoft 365 CSP perspective, which we deal with daily, inactive users often continue consuming paid licenses long after departure.
- Operational confusion Emails, approvals, and system alerts may continue routing to someone who no longer works for you. The longer an account stays active, the more expensive the cleanup becomes.
- Your offboarding checklist that actually works If you want an offboarding process that holds up under real world pressure, it needs to be standardized and repeatable. This is the baseline we recommend to clients across California.
Remediating these issues is as simple as a step by step process outlined below:
Identity and access
- Disable the user in Entra ID or your directory immediately
- Revoke all active sessions and tokens
- Remove MFA methods tied to personal devices
- Remove group memberships and admin roles
- Convert mailbox or archive as needed
Email and collaboration
- Set mailbox forwarding if business continuity requires it
- Assign mailbox and OneDrive ownership
- Remove from Teams, SharePoint, and distribution lists
- Review inbox rules and external forwarding
Devices and endpoints
- Collect company owned hardware
- Remove device from Intune or MDM
- Wipe or reset as appropriate
- Verify no unmanaged personal devices retain access
Network and remote access
- Disable VPN accounts
- Remove remote management tools
- Rotate any shared credentials
- Review firewall and WiFi access lists
Licensing and billing
- Remove or reassign Microsoft 365 licenses
- Validate billing alignment in CSP or direct
- Document the change for audit trail
If this feels like a lot, that is because it is. Mature environments automate most of this.
Timing matters more than you think
One of the biggest mistakes we see is delay. Offboarding should begin the moment HR confirms separation, not days later.
Best practice is:
- Immediate access disable as soon as termination discussions are over
- Same day device and license review
- 24 hour validation sweep across key systems
In environments using Entra ID, Conditional Access, and centralized device management, this can be largely automated. In fragmented environments, it becomes manual and error prone. This is where many SMBs get into trouble.
How to future proof your offboarding process
If you want this to stop being a fire drill every time someone leaves, focus on three structural improvements.
- First, centralize identity. The more systems tied to Entra ID or your primary directory, the easier clean removal becomes.
- Second, automate wherever possible. PowerShell, Graph automation, and lifecycle workflows dramatically reduce human error. This is exactly why many MSPs, including Valley Techlogic deployments, invest heavily in standardized offboarding runbooks.
- Third, require HR and IT alignment. Offboarding failures are often communication failures. A simple, enforced workflow between departments eliminates most risk.
The bottom line is cybersecurity is not only about stopping outside attackers. It is about maintaining control of your own environment. A single overlooked account from a past employee can quietly undermine your security, your compliance posture, and your licensing costs. If your offboarding process lives in a checklist on someone’s desktop or depends on memory, it is time to tighten it up.
At Valley Techlogic, we help organizations across California turn offboarding into a controlled, repeatable process that closes risk instead of creating it. If you are not completely confident in your current process, now is the right time to review it. Learn more today through a consultation.

This article was powered by Valley Techlogic, leading provider of trouble free IT services for businesses in California including Merced, Fresno, Stockton & More. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on X at https://x.com/valleytechlogic and LinkedIn at https://www.linkedin.com/company/valley-techlogic-inc/.