In addition to major updates released for Microsoft Windows this month, Microsoft also released their Digital Defense Report for 2023. You can find it here.
One page in the report caught our eye and that’s the five items you can enable that will block 99% of attacks. At the top of the list is enabling multi-factor (MFA). The other four items are: apply Zero Trust principles, use extended detection response (XDR) and anti-virus/malware, keep your systems up to date and protect your data.
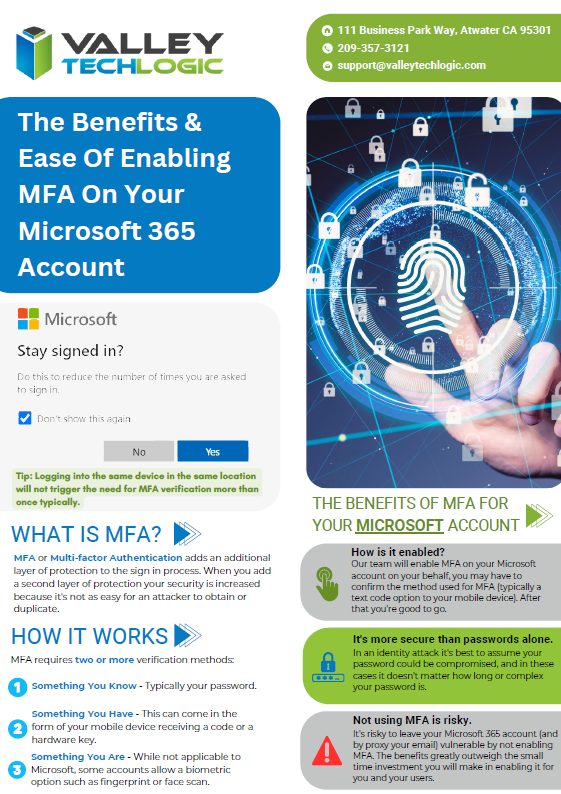
We’re zeroing in on enabling MFA today as it’s simple to implement (can be done today) and will increase the security of your account tenfold.
The reason we say this is because the report also outlined that password-based attacks are also up tenfold, from 3 billion attempts per month in 2022 to 30 million per month in 2023. Microsoft says they have blocked an average of 4,000 password attacks per second over the last year. Attacks know many Microsoft users have not enabled MFA and are targeting those users specifically.
It’s not a manual process either, many of these brute force attempts are being enacted by bots. Cyber criminals set these bots up and let them run, reaping the rewards from the stolen accounts they’re able to access. In addition to that, many credentials are still available on the web for a very low cost.
We know many people have “breach fatigue”, news of yet another massive breach is not the major news topic it once was. It can feel much different though when it happens to you directly. If you currently re-use passwords for your accounts, it’s highly likely that password has been offered for sale on the web.
Enabling MFA is strong protection against these methods and more. See our chart on how to set up MFA for your own Microsoft account.
 As you can see, it’s pretty easy to enable MFA for your own account but did you know you can also set it up from an organizational level to enable it for your employees?
As you can see, it’s pretty easy to enable MFA for your own account but did you know you can also set it up from an organizational level to enable it for your employees?
The steps doing that are as follows:
- Navigate to the Microsoft 365 admin center at https://admin.microsoft.com.
- Select Show All, then choose the Azure Active Directory Admin Center.
- Select Azure Active Directory, Properties, Manage Security defaults.
- Under Enable Security defaults, select Yes and then Save.
Just to note, you must turn off legacy per-user MFA first before enabling global MFA in your organization. You can find that by navigating to Users > Active Users and you should see a tab on this page for multi-factor authentication. On this page should be a list of your users and you want to set each user to MFA disabled. Then you can loop back to our previous instructions and turn on the global MFA instead.
There are also other global security settings in this section but before testing out different settings we suggest reaching out to your IT provider. MFA is a pretty non-intrusive security setting, but other settings may have unexpected consequences when it comes to you or your employee’s workflow. It’s best to evaluate your security options with a pro.
Don’t have access to an IT pro? Valley Techlogic can assist. We are experts both in the field of cyber of security AND all things Microsoft. See our advertising flyer on our approach to enabling Microsoft 365 MFA for our customers.
 You can schedule a consultation with us today to learn more.
You can schedule a consultation with us today to learn more.
Looking for more to read? We suggest these other articles from our site.
This article was powered by Valley Techlogic, an IT service provider in Atwater, CA. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on Twitter at https://x.com/valleytechlogic.

