Now that it’s 2024 we’re reflecting on the biggest events in tech that occurred in 2024, and in today’s article we want to talk about the biggest cyber security breaches that occurred in 2023.
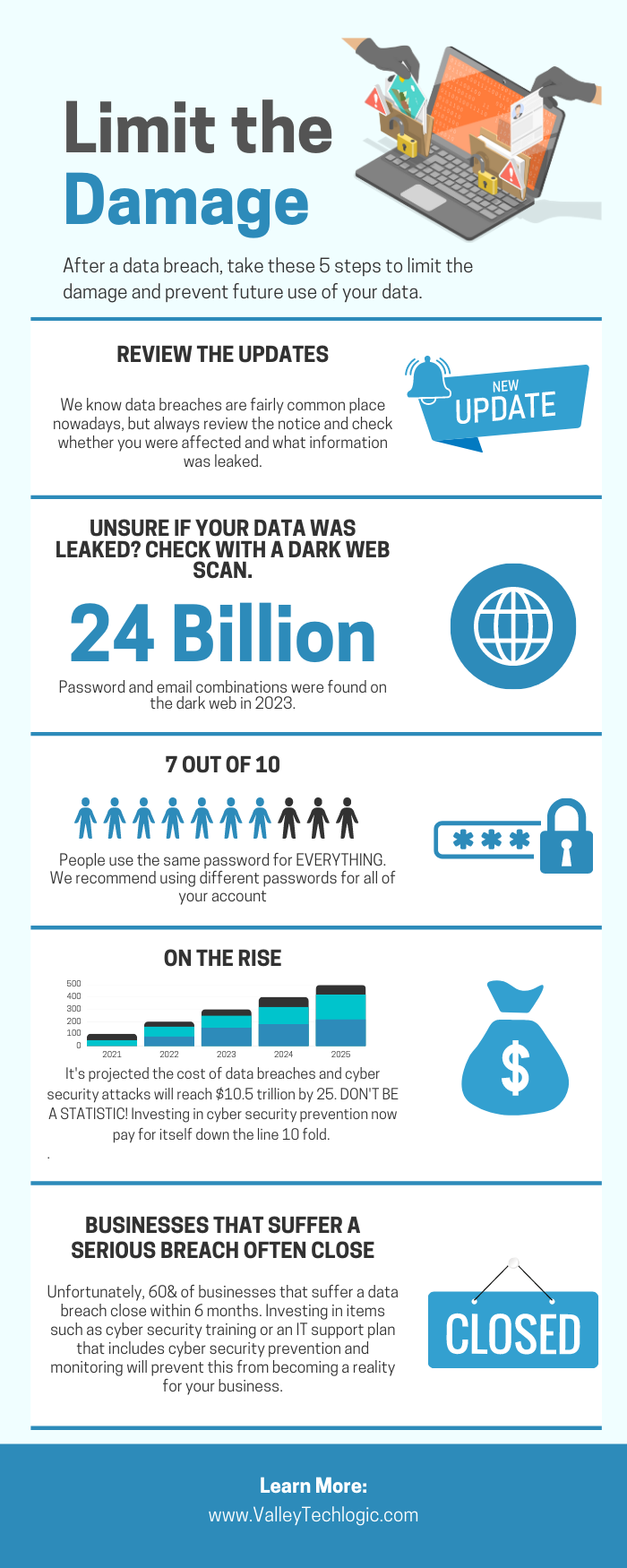
Before we get into it, let’s talk about the hard numbers. Across the board, cyber threats are up year over year and 2023 was no exception. Here are 8 eye opening statistics on cyber threats as of writing:
- The global average cost of a data breach is $4.45 million and a ransomware attack $5.13 million as of 2023.
- The average lifecycle (discovery to remediation) of a data breach is 277 days.
- 74% of data breaches still involve a human element in 2023.
- 64% of Americans have not checked to see if there data has been lost in a data breach.
- Almost half (46%) of all cyberattacks were on US targets.
- More than 1 million identities were stolen in 2023.
- 30% of those people were a victim of a data breach in 2023.
- 54% of office works express feeling “cybersecurity fatigue” in regards to news of data breaches.
Unfortunately, public apathy towards cybersecurity preventions from ongoing, sustained attacks and the lucrative nature of successful attacks performed on business entities makes for a potent recipe in these attacks only continuing to increase in 2024.
We want to take a look back at the biggest breaches that occurred in 2023 and also present our solution for preventing an attack of this nature from occurring to your business.
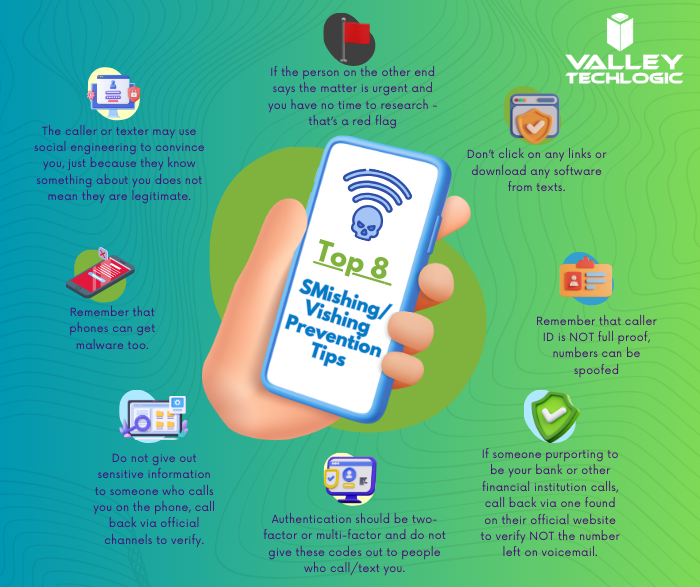
- MGM – Occurring in September, the unusual way MGM was breached made headlines because it did not initially involve a computer. Instead, attackers posed as people of importance to the company via a phone call and gained access to their systems, causing a loss of reputation, $100 million in damages, and 5 class action lawsuits to be filed.
- ChatGPT – Not even AI is safe when it comes to targeted attacks from hackers, in March of 2023 a bug in their source code exposed the personal information of a 1.2% of their Plus Subscribers including home addresses, full names and email addresses.
- MOVEit File Transfer System – The fallout from this breach that occurred in June 2023 extended far beyond the file system management software company itself, including California’s biggest pension fund holders CalPERS and CalSTRS.
- RockStar – RockStar is another example like MGM that proved hackers don’t need expensive equipment to breach insecure systems, with this breach being conducted using a cellphone, a hotel room TV and an Amazon FireStick.
- The City of Oakland – An entire city was the target of a hack that occurred in February of 2023, the sustained attack which lasted more than a week prompted the city to even declare a state of emergency while systems remained offline. Class actions lawsuits were also filed in the aftermath of the attack in this case.
These are just five attacks that made major news last year, but there were thousands more that did not make major news. When an attack occurs on a small business many times it leaves the owners with no choice but to close up shop (60% of small businesses that are the victim of a cyber attack close within 6 months).
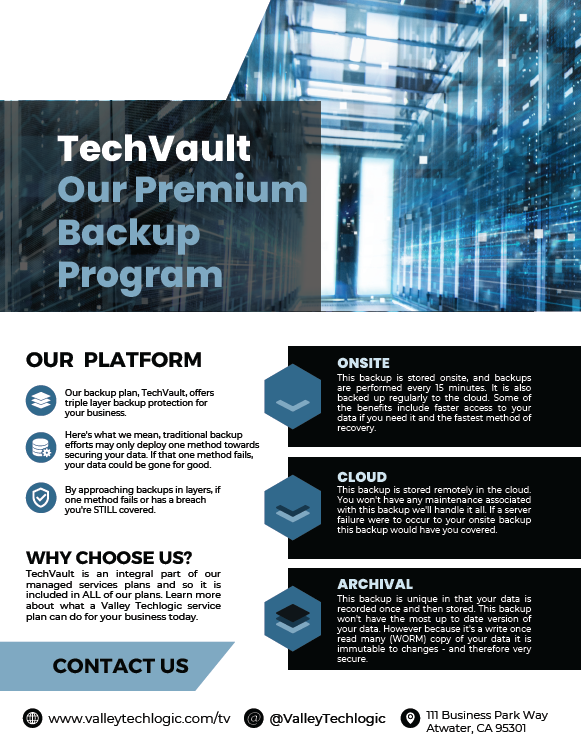
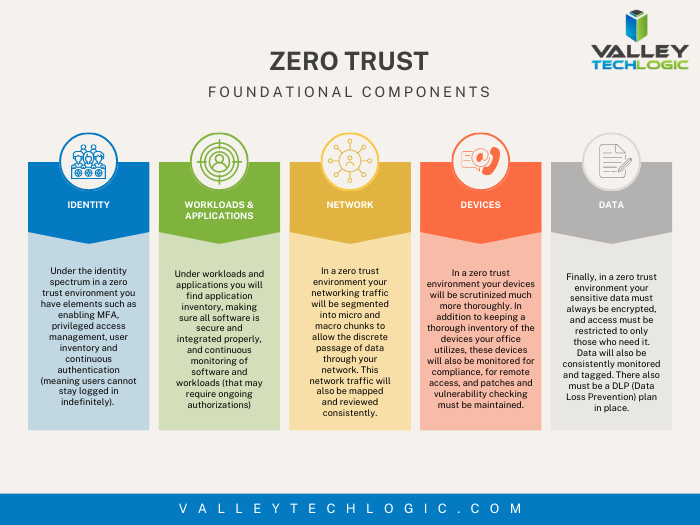
As IT providers it’s a frustrating topic for us as so much of this is preventable. If more preventions were put in place and it was more difficult for attackers to realize their goals than it would have a cumulative positive effect overall. As the saying goes, an ounce of prevention is worth a pound of cure. Let us help you meet your cybersecurity goals in 2024 by clicking on the image below.
 Looking for more to read? We suggest these other articles from our site.
Looking for more to read? We suggest these other articles from our site.
This article was powered by Valley Techlogic, an IT service provider in Atwater, CA. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on Twitter at https://x.com/valleytechlogic.