If you’re not aware, phishing is another word for scams perpetrated over email. It was coined in 1996 and was first associated with hackers attempts to steal America Online (AOL) accounts, and it has not slowed down since then.
As of 2021 most hacking attempts are phishing scams, the phrase is meant to evoke the image of a hacker literally fishing for their victims by baiting a hook which in this case is a credible looking email from a place you might actually do business from, a colleague or a family member. 94% of malware attempts originate from an email sent to the victim.
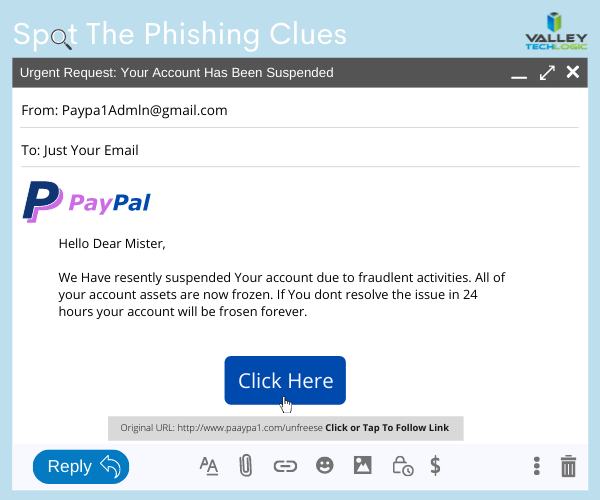
Well as credible as they can manage, many phishing attempts are poorly worded and grammatically incorrect as the senders are from another country from the victim. In the image below we showcase a phishing email you might receive, click to reveal the answers.
Not all phishing attempts will be so obvious though, here are our 10 tips to avoid falling for a phishing scam.
- You are asked to reply with sensitive details. A legitimate business will never ask for your private details via email, if you’re unsure contact the business directly to ask.
- The message says you must respond urgently or face dire consequences. Legitimate businesses such as the financial institution you bank with won’t relay an important message over email alone, and they’ll never threaten you.
- The email contains a non-standard email attachment. While even standard email attachments can contain malware, a non-standard email attachment is a clear sign something is amiss.
- The senders email address doesn’t match the contents. As in our example, a legitimate business (especially a large one) won’t be using a gmail address. You also want to watch out for slight misspellings, such as an email coming from admin@paypa1.com
- The email contains an unusual request. You receive an email that looks like it’s from your boss, and he’s saying he wants to reward some key players in your company by gifting them gift cards from a popular big box store. He says not to give them to the players directly, simply reply with the gift card numbers and he’ll handle it. This is just one example of a scam we have unfortunately heard of happening. If the email is requesting large amounts of money be spent in unusual way or private details be sent over email, even if the email looks legitimate you should verify with the supposed sender first.
- It has an attachment you weren’t expecting. If receive an email with an attachment and the body suggests you requested information, but you don’t remember doing so, it’s probably a phishing scam.
- The email says you won a prize, but you must enter your banking information to claim it. Prizes are a common phishing scam trope; they may also try to get you to download a suspicious attachment.
- The URL in the email doesn’t match the business it claims to come from. As in our example, phishing attempts often involve a similar but not quite right URL. Many scammers will try to gain the victims trust by sending them to an “official” looking website where they will login with their legitimate credentials, allowing the scammer to gain access.
- The content is canned. Many phishing scammers reuse the materials of others. One example is you receive a suspicious sounding email, such as someone saying you have stolen their copyright images and you must visit a website to confirm. If you Google the email you may find examples of others online who have received that same
- The greeting doesn’t match the content. This is a simple one, if you receive an email supposedly from your boss but the greeting starts with “Dear” or another out of character greeting, it’s probably a phishing attempt.
This is only a start, many phishing attempts are highly sophisticated and difficult to spot but knowing some of the signs will help you be more attentive to things that may be wrong with an email you receive. We also have found for our clients, randomized simulated phishing attempts can help them with training their staff to keep an eye out for phishing attempts.
Most successful hacking attempts involve a human element, training is your only first line of defense. If you would like to increase your defense against phishing attempts, malware, ransomware and more, Valley Techlogic can help. Schedule an appointment with us today to learn about our comprehensive cyber security packages for businesses.
Looking for more to read? We suggest these tech articles from the last week.
-
How to (hopefully) restore your Gmail account if you lose access – The Verge
-
Microsoft, Facebook and everyone else are building the metaverse. Will you want to live there? – CNet
-
Volume of cyber intrusion activity globally jumped 125%: Accenture – ZDNet
-
Passwordstate customers complain of silence and secrecy after cyberattack – TechCrunch
-
Let’s Get Physical As China EV & Clean Tech Rises – Forbes
This article was powered by Valley TechLogic, an IT service provider in Atwater, CA. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on Twitter at https://x.com/valleytechlogic.