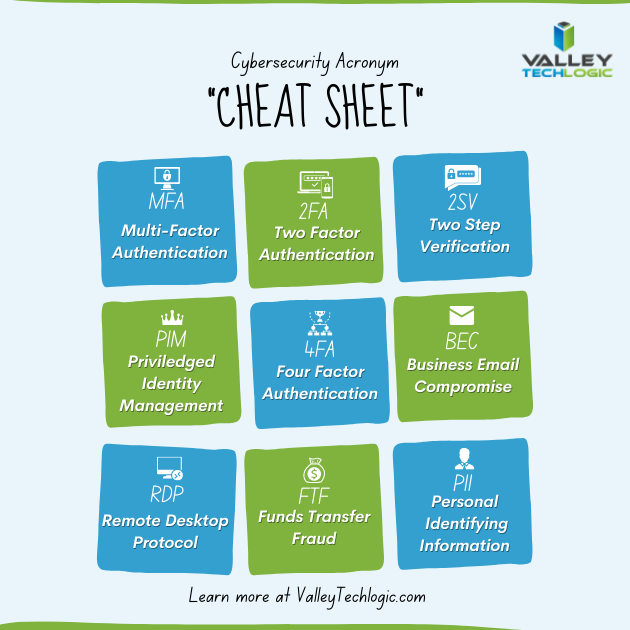
Explaining cyber security in 2024 means navigating all sorts of buzz words – cybersecurity awareness, data breach, ransomware and malware, endpoint security, threat detection, two-factor and multi-factor authentication, and yes zero trust just to name a very small portion of them.
We know users feel burnt out on the number of phrases that do represent actual security threats that are thrown at them day to day, as an IT service provider it can be difficult to translate this phrasing into a tangible concern for our clients.
For example, whose data hasn’t been leaked in a data breach in 2024? Our personal data has become a commodity that most of us have accepted may end up on the internet in ways we can’t anticipate or prevent.
But that’s not exactly true, with a zero trust environment you can make your business much more resilient to threats and data breaches and it’s not as difficult as you may think.
What is Zero Trust? Zero Trust abandons the idea that everything connected to your work network is safe and instead treats everything as a potential threat, you might be thinking now, why would I want that? It is a more rigorous approach but extremely beneficial, if every device must be individually verified then none of them can act as a trojan horse to your business.
The key pillars of Zero Trust are:
- Least Privilege: Users get enough access to do their job, no more no less. We can’t tell you how many situations we’ve encountered where everyone’s computer has admin level privileges, and in a data breach situation that would make any one of those devices an extreme threat to your business.
- Continuous Verification: It might be kind of irritating at first to check your two-factor application or your phone for a texted code – but the benefits will come in spades should any of your passwords be leaked (only around 50% of users are aware of good password hygiene).
- Network Segmentation: This one is not too difficult to implement, and your users won’t even notice it, this is just segmenting your network so that say your work computers and other devices are on one network and outside devices (like a visitor’s cellphone) are on something like a guest network. This zero cost fix will mean you have greatly reduced exposure to threats from outside devices.
Within the pillars it’s easy to see the three steps we would recommend someone start with when setting up a zero trust environment, that is reducing users to having only the level of access tey need, enforcing two factor or multi-factor authentication, and setting up at the very least a guest network.
When it comes to implementing cyber security standards, the sky is the limit. All of the settings we recommend above really only cost time, but they will benefit your business greatly in the event any kind of breach occurs.
Limiting the damage that can be done is always the goal when it comes to cyber security, hackers will constantly push at boundaries and find ways to access your systems (yes even if you’re a small business) and with minor improvements you can protect yourself from most major threats.
Cyber security protection is a cornerstone of our service plans, and whether you’re interested in evolving your cyber security standards to include zero trust strategies or in receiving the benefits of a comprehensive cyber security stack without having to assemble it yourself, Valley Techlogic has you covered. Book a meeting with us today to learn more.
Looking for more to read? We suggest these other articles from our site.
-
Apple releases their new M4 chip and it’s getting rave reviews, also considering the benefits of Apple vs Microsoft for your office
-
Are you sure you can count on your data backups? 5 ways to confirm your backups are working (and avoid the 37% data backup failure rate)
-
Frontier Communications suffered a cyber security breach last week that shut down their systems
-
The 6 roles you would you need to fill to match the services delivered by an outsourced IT vendor
This article was powered by Valley Techlogic, leading provider of trouble free IT services for businesses in California including Merced, Fresno, Stockton & More. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on Twitter at https://x.com/valleytechlogic and LinkedIn at https://www.linkedin.com/company/valley-techlogic-inc/.





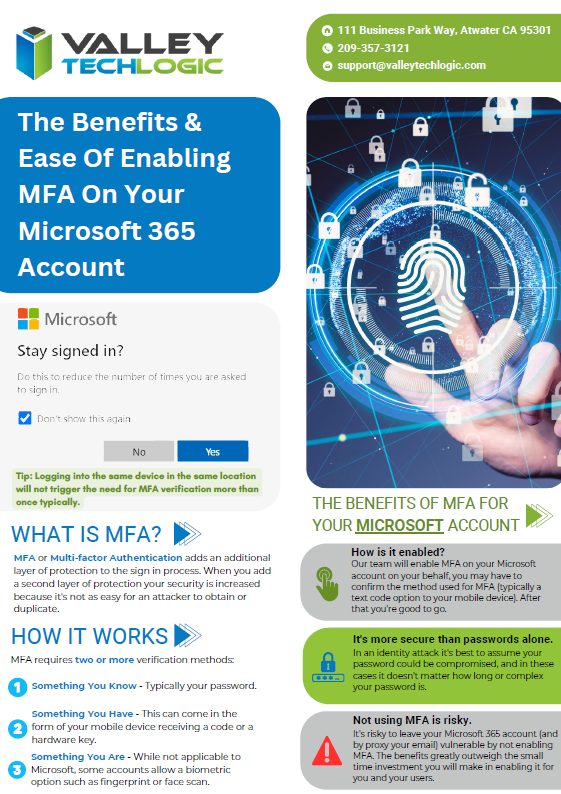



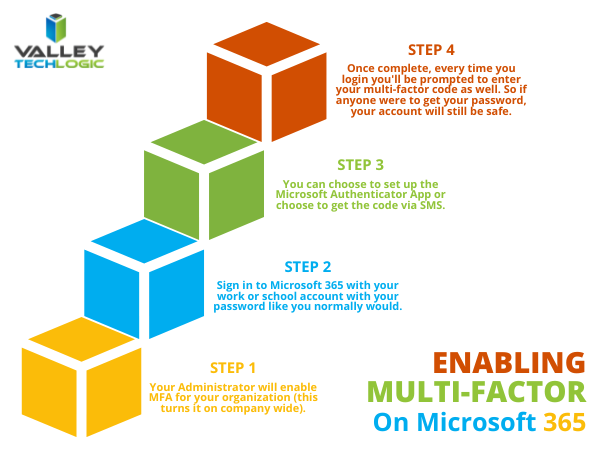

 With breaches being ever more common, having that additional step past just a password before a hacker can access your account can make all the difference. A password you use across multiple website (which is also a bad idea) may be leaked without you even being aware of it, and the prompt from a multi-factor authentication application may even be your first clue that your accounts are being accessed by someone other than yourself.
With breaches being ever more common, having that additional step past just a password before a hacker can access your account can make all the difference. A password you use across multiple website (which is also a bad idea) may be leaked without you even being aware of it, and the prompt from a multi-factor authentication application may even be your first clue that your accounts are being accessed by someone other than yourself.
