If you’re a contractor or subcontractor for the Department of Defense (DoD) you probably at least have an awareness of the evolving situation surrounding the CMMC (Cybersecurity Maturity Model Certification) program, or maybe you’ve even begun the self-assessment process.
Announced summer of 2019, version 1.0 was released January 31st, 2020, and a 5 year roll out was planned to get DoD contractors and subcontractors compliant with the framework. The framework is based on the security controls found in the National Institute of Standards and Technology (“NIST”) Special Publication (“SP”) 800-171, with many of the security controls found in CMMC having a direct correlation to a control found in NIST 800-171.
While the initial CMMC framework was aimed at bringing defense contractors up to speed in their cybersecurity efforts to protect critical Controlled Unclassified Information (CUI), the use of the broad term CUI instead of the defense specific Covered Defense Information (CDI) phrase may indicate that this framework will extend beyond just defense contractors in the future.
The controls found in NIST are applicable to businesses of all sizes and in all sectors so following the CMMC or NIST frameworks whether or not you’re defense contractor/subcontractor will mean your business will be well protected and compliant with rules and regulations set by your vendors, clients, and services for your business such as cybersecurity insurance.
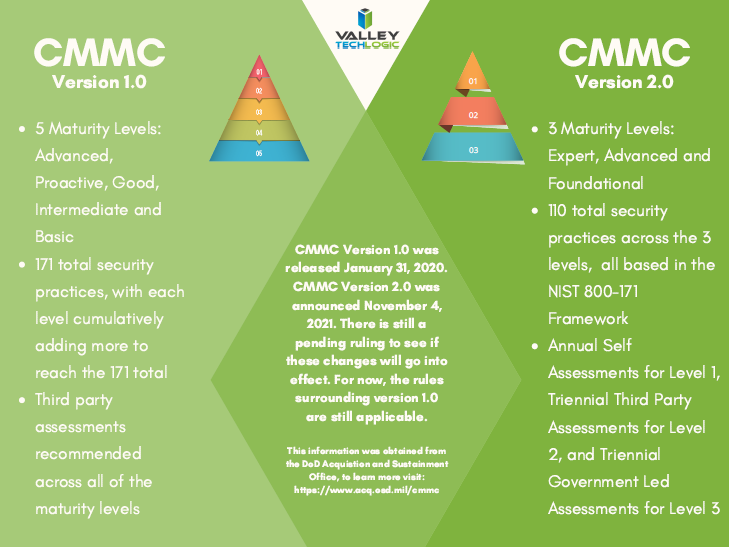
In it’s original iteration there were 5 maturity levels found in CMMC, with levels 1-3 really closely following NIST and 4-5 going beyond the scope of what NIST covers. They were described as “maturity levels” as they were meant to measure the maturity of the cybersecurity practices found within your organization.
For most defense contractors, reaching level 3 of CMMC would be an ideal goal. Levels 4 and 5 covered practices outside the scope of most business’s and would require more specialized (and expensive) security practices. Even in version one of CMMC contractors were allowed to self-certify for maturity level 1, but beyond that would require outside certification. The waiting list to receive that certification is long, so planning to implement the required cybersecurity measures and getting on the waiting list to be certified ASAP is a good idea.
Now, as of November 4th the DoD has announced an update to CMMC. Version 2 may be removing two of the levels and some of the security measures that were unique to CMMC framework, making the framework match NIST even more closely. Below is the chart we have created with the outlined changes as we know them and as of this posting.
This is an evolving situation and as the rollout progresses it’s imperative that businesses that receive DoD contracts begin or continue to increase their efforts in becoming CMMC certified, which may mean drastically increasing your cybersecurity efforts across the board.
Valley Techlogic has experience in helping businesses meet the goals found within the CMMC framework and we’re ready to help your business meet your certification and cybersecurity goals today. Click here to schedule a quick consultation to find out more.
Looking for more to read? We suggest these other articles from our site.
-
The Dirty Loophole That Lets Insurance Companies Refuse to Cover a Cybercrime Theft in Your Business
-
Windows 11 is out, should you upgrade?
-
What does the California data breach notification law mean to your business?
-
3 Reasons You Want to Offer Cyber Security Training to Your Employees
This article was powered by Valley TechLogic, adns, n IT service provider in Atwater, CA. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on Twitter at https://x.com/valleytechlogic.

