Yesterday, a number of LastPass users received alarming alerts in their email inbox that their passwords – including their master password – had been compromised. The news quickly spread across the internet, starting with forums, and then making its way to Twitter where it was picked up by larger news outlets.
LastPass immediately denied that a breach had occurred within their organization and at first indicated that the alerts were happening to users who were the victims of “credential shuffling”. That means these users had reused their passwords on other websites who may have had a breach in the past, and now bots trolling the internet for compromised accounts have stumbled upon their password vault credentials.
This didn’t end up being the case either, but it is a good reminder NOT to password shuffle, especially with the master password for your password vault (if any password should be unique – it should be that one).
As of this morning LastPass determined that the alerts were sent in error by systems that were set up to be too stringent. They’ve indicated they now adjusted the alerts systems so inaccurate alerts will not be sent again. They also clarified that they don’t store user passwords on their own servers, and that they work on a “zero knowledge” security model which means they are not able to see your master password at all.
The fact that this news took off in a flash may be indicative of the heightened awareness users have around the security of their data, especially those who currently use a password manager as part of their security repertoire. Even if the alerts occurred in error that may be cold comfort to the scare those users experienced.
To us, it’s a reminder that the best cybersecurity efforts are multi-layered. We believe it’s equal parts implementation of security measures, monitoring of those measures, and behavioral changes on the part of the users.
Even if the alerts that occurred yesterday were the result of a system issue not a security issue, we think the users that responded had the right idea when they chose to investigate. It’s also a good idea to change your password if you get a security alert, even if it turns out to be a false alarm. It won’t hurt anything to take that extra step to protect yourself, the old adage “Better Safe Than Sorry” rings especially true when it comes to cybersecurity threats.
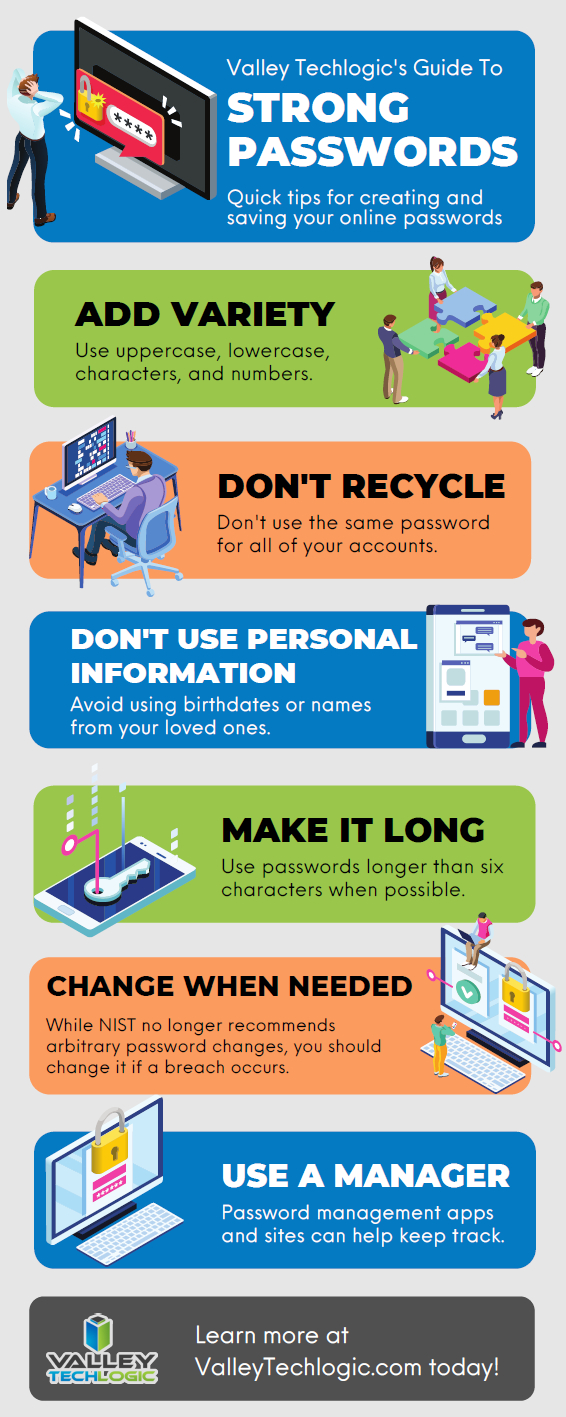
We created this resource on the topic of good password hygiene that you can keep to review, or even pass along to your co-workers/employees.
Finally, even if the unthinkable occurs and your passwords are leaked, again a multi-layered approach will protect you. You should enable 2-factor/multi-factor authentication when and where you can. So if someone does get your password somehow, they still will be blocked from logging in.
If the security measures in your workplace aren’t up to snuff or you’re interested in cybersecurity training for your employees, Valley Techlogic can help. Boosting the security measures for your business and providing a digestible cybersecurity training program for your employees is included as part of our technology service plans. Schedule a free consultation with us today to learn more.
Looking for more to read? We suggest these other articles from our site.
-
Hackers and the holidays, US government warns ransomware doesn’t take days off
-
Grab our 2021 HIPAA compliancy checklist and see how you can address HIPAA in the New Year
-
High Tech Holidays – Five Ways Technology Can Make Your Holiday Season Easier
-
Windows 11 system requirements – Will your computer be able to run it?
This article was powered by Valley TechLogic, IT service provider in Atwater, CA. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on Twitter at https://x.com/valleytechlogic.

