In what is truly the 11th hour (inauguration day for President Trump is January 20th, 3 days from now at the time of writing), the Biden administration announced an executive order that looks to strengthen US cyber defenses against outside influence, particularly from Russia and China.
Described as a “sweeping” move, the executive order covers topics from cyber threat vulnerabilities to guidance on consumer electronics and even outer space.
The order gives enhanced authority to CISA (Cybersecurity and Infrastructure Security Agency) to hunt for threats on federal networks, likely a response to the recent news that President Trumps communication with Vice President JD Vance may have been compromised by Chinese hackers.
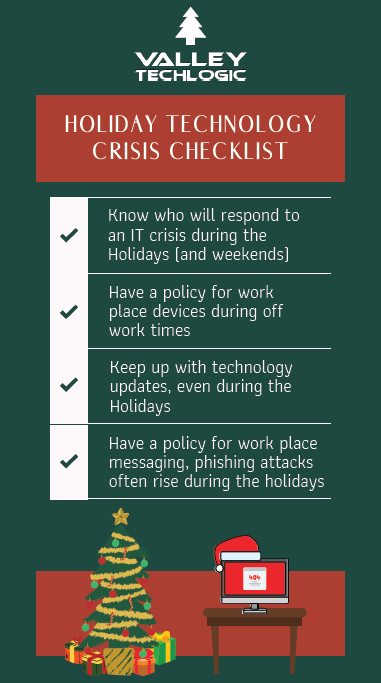
The order also covers additional protections for Federal agencies, including implementing end-to-end encryption for all video and email communication and stating that by 2027 any internet connected devices purchased for federal use must have a “cyber trust mark” indicating they meet current cyber standards. Internet connected devices have a wide range of criteria in 2025, everything from home security systems to our appliances has an internet connected option in our modern world.
The order also covers requiring enhanced cybersecurity measures for our space systems, likely in response to Russia targeting Ukraine’s satellite systems in the ongoing invasion.
The order even takes aim at Microsoft specifically, citing a host of errors that allowed Chinese attackers to breach their networks in 2023 which had downstream consequences for our federal government (senior US officials email accounts were allegedly breached in the aftermath of the attack).
Trump’s team has not yet responded to the new executive order so it’s unclear how much follow through will be had on it once he regains office next week, however the Biden team is optimistic on its longevity as bolstering US cyber defense was also a goal during the initial Trump administration (CISA was created in 2018 under Trump’s first term).
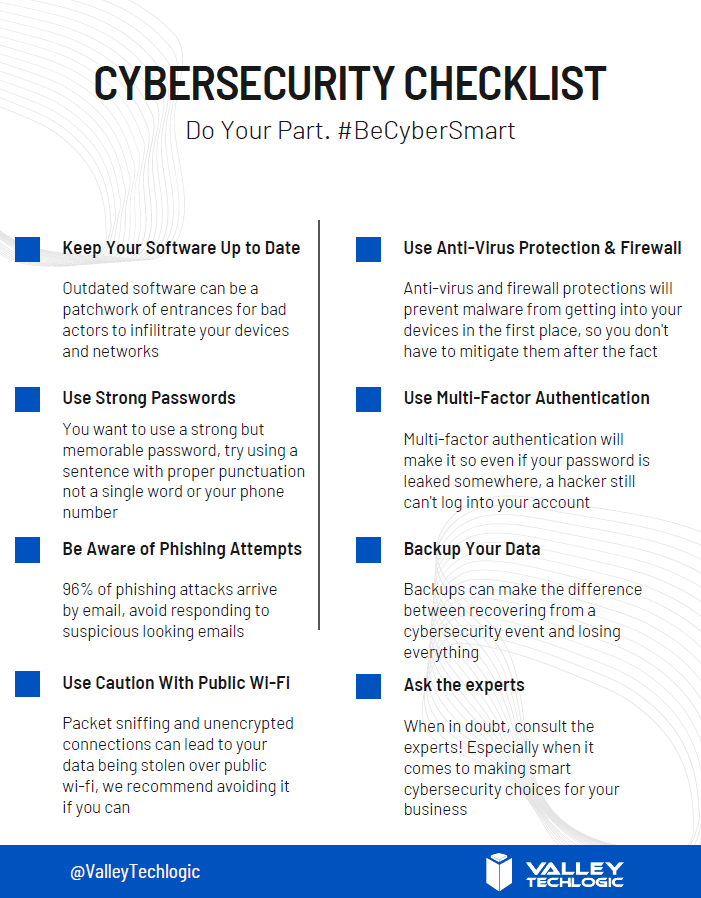
As our government looks to shore up their cybersecurity practices in 2025, what are you doing to ensure your business is protected from ongoing threats?
Cyberthreats are not limited to large scale attacks on larger businesses, small businesses are often seen as “easy targets” and can also be swept up in the aftermath of an attack aimed at someone else.
Implementing strong cybersecurity measures, such as secure passwords, regular software updates, employee training, and robust data encryption, not only protects the business but also builds trust with customers. It is clear, in 2025 cybersecurity is no longer a topic that can be pushed off until a later time. The threats are here now and the time to act is before your business is compromised, because afterward it might be too late.
Valley Techlogic includes cybersecurity protection as a core offering in all of our customized service plans. Learn more today with a free consultation.
Looking for more to read? We suggest these other articles from our site.
-
Are cyber attacks still being conducted the same way in 2025? Top 8 cyber attack methods explained
-
Windows 10 reaches EOL October 2025, and those who don’t upgrade may have to pay
-
5 technology predictions for 2025 (and where to invest your tech spend in the New Year)
-
Is physical security a priority for 2025? Our recommendations for choosing security cameras for any scenario
This article was powered by Valley Techlogic, leading provider of trouble free IT services for businesses in California including Merced, Fresno, Stockton & More. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on X at https://x.com/valleytechlogic and LinkedIn at https://www.linkedin.com/company/valley-techlogic-inc/.