While it’s just now being reported on, the DDoS attack on Google Cloud occurred on June 1st and lasted for 69 minutes – reaching a peak of 46 million requests per second.
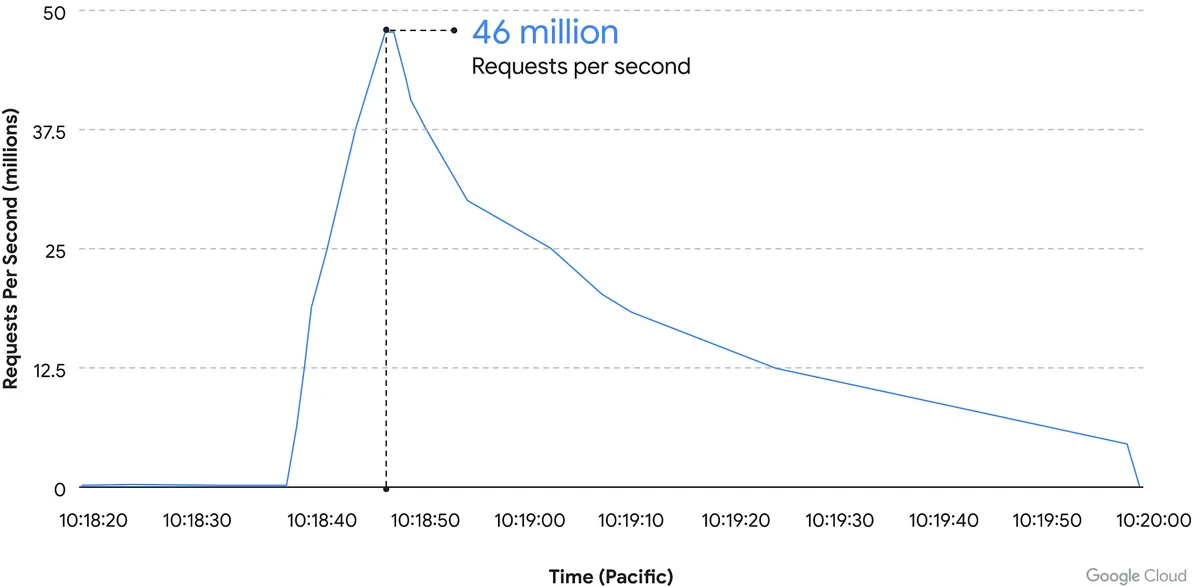
We’ve covered Distributed Denial of Service (DDoS) attacks before in this blog, but the scale of this one is mind boggling. It’s nearly twice the size of Cloudflare DDoS attack from last year around this same time, which peaked at 26 million requests per second (sent from just over 5000 devices).
If you’re wondering where the devices used in these attacks originate from, the answer in this case is unsecured devices. Specifically compromised Mikrotik routers.
There’s been a number of articles regarding possible compromises to the Mikrotik brand of router including one instance that involved over 200,000 devices. Many in the security space wondered if there would be a fallout from that and now, we have our answer.
However, what’s more impressive is not the scale of this attack, but the fact that it was successfully blocked by Google.
Botnet attacks of this nature are not rare, it’s difficult to say exactly how many attacks occur per day but it has been noted they’re on the rise since the Russian invasion of Ukraine. A botnet is essentially an assembly of compromised devices that are used to attack a target. DDoS attacks are one of the most common uses, but they’re also used for phishing, cryptomining, or to bruteforce passwords just to name a few. The largest botnet ever recorded belonged to Russian BredoLab and consisted of 30,000,000 devices.
Would be bad actors can even purchase DDoS as a service for as little as $5 per hour which should give you an indication how prevalent and common they are as an attack vector.
Google blocked this attack by leveraging their Cloud Armor product, a network security service directly aimed at preventing DDoS attacks. If they were looking for a powerful case study for the effectiveness of this product, we can think of no better example then effectively blocking the largest DDoS attack in history (so far).
Part of blocking a DDoS attack is early detection. DDoS attacks ramp up, if you can detect an incoming flux of peculiar traffic to your network you can block the attack before it’s able to scale up and cripple your network.
Besides blocking potential attacks, the other side of the coin is not becoming an unwilling participant in a botnet through a compromised device in your home or business.
The sinister part of it is you may not even be aware your device is compromised and it’s not just mobile devices and personal computers that can be affected, even IoT (Internet of Things) devices can be hacked. There are a few things you can do to prevent your devices from being taken over by hackers as we outline in the chart below:
 If your business needs assistance with protecting from any potential attacks or making sure your devices stay uncompromised, Valley Techlogic can help. All of our plans include robust cybersecurity protections at no additional charge, including assisting in your cyber security training goals (after all, human error is the #1 cause of data breaches). Schedule a consultation today to learn more.
If your business needs assistance with protecting from any potential attacks or making sure your devices stay uncompromised, Valley Techlogic can help. All of our plans include robust cybersecurity protections at no additional charge, including assisting in your cyber security training goals (after all, human error is the #1 cause of data breaches). Schedule a consultation today to learn more.
Looking for more to read? We suggest these other articles from our site.
-
5 Tips for Conquering Email Spam (and Phishing) in 2022
-
Five Email Migration Tips & Reasons We Suggest You Make that Move for Your Business
-
CMMC Series: The Consequences for CMMC Non-Compliance
This article was powered by Valley Techlogic, an IT service provider in Atwater, CA. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on Twitter at https://x.com/valleytechlogic.

