Video game news might fall outside our normal wheelhouse but reporting on cybersecurity events is right up our alley, and this the most recent hack on major game developer Rockstar Games made major news over the weekend so we wanted to chime in with our thoughts.
The hacker going under the moniker “Tea Pot” released video clips of Rockstar Games unreleased (and previously unannounced) new game, Grand Theft Auto 6. The clips revealed spoilers on the games content and also showcased rougher assets as the game is still in early development, something game publishers don’t ordinarily highlight.
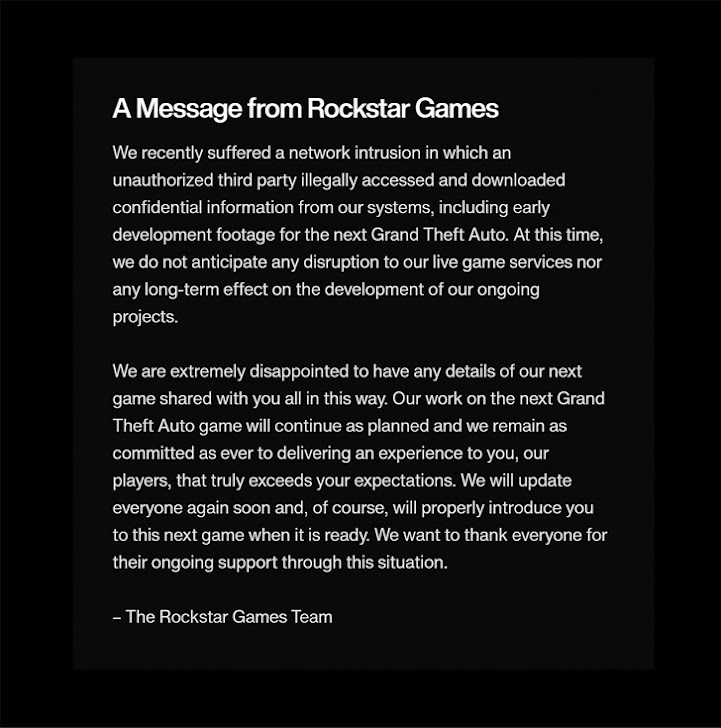
In a message acknowledging the breach the Rockstar Games Team had this to say:
The hacker returned after releasing the data and sent a message on the GTAForums claiming they wanted to “negotiate a deal” with Rockstar Games, hinting that they had more data to release. Speculation proliferated across the internet that the hacker had somehow obtained some of the games source code.
With the source code portions of the game could be re-engineered (outside Rockstar Games) and that could even possibly be used to provide at least a semi-playable version. The fallout from that would be devastating as it would steal the developer’s agency in releasing their own content and also reveal trade secrets that could be used to help create knockoff or pirated versions.
Rockstars parent company, Take-Two, has issued take down notices to social media accounts and Youtube channels broadcasting the stolen footage as work to perform damage control. There will probably be a costly investigation into the origination of the hack and there may even be financial complications beyond that, as investors may question what effect this leak will have on the eventual release of the game.
This hack is a perfect example of the reputation cost associated with being hacked. Recovering data you need to do your day to day job is one aspect, but you also need to think about data you wouldn’t want released to the public.
Projects that haven’t been announced yet or information that’s not easily changed (tax information, personal identifying information) are just two factors, but there’s also the release of your customers private data. Many aren’t aware a breach involving client information can even lead to legal ramifications depending on regulatory factors in your sector.
There’s also your private emails or messages, which could have future business plans, personal information, or other things that could be used by the hackers in a ransomware attempt (or even ongoing blackmail).
Cybersecurity prevention’s are important but one element that has surged to the forefront of our minds is a recovery tool that’s becoming more difficult to obtain – cybersecurity insurance.
You can review our comprehensive guide on the topic but here’s a brief chart on what cybersecurity insurance typically covers:

Obtaining coverage can be challenging, the requirements have grown much steeper as cybersecurity attacks become more common place, and that doesn’t look like it’s going to change anytime soon. At Valley Techlogic we have experience in helping clients obtain coverage so if the unthinkable does occur, their business will survive the hit.
Whether you’re are in the early stages of researching cybersecurity coverage or if you have an application form in front of you, we can be your guide through the process. Schedule a consultation today to learn more.
Looking for more to read? We suggest these other articles from our site.
This article was powered by Valley Techlogic, an IT service provider in Atwater, CA. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on Twitter at https://x.com/valleytechlogic.